The internet has been abuzz with the concerning news that ISIS has released a list of US military personal and calling on radical Muslims to attack them. The solution to this problem is simple – Arm our service members…
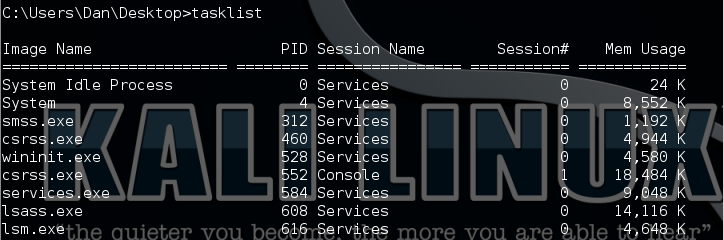
Contrary to the ISIS claim that the list of service personal released was obtained by hacking military servers, in actuality the list was most likely gleaned from military press releases using nothing more advanced than Google. In all actuality, it is very trivial for someone with even the most basic Open Source Intelligence skills to find out a ton of information on a person including where they live using Open Source Intelligence (OSINT) programs.
The problem with open source intelligence is that the information discovered is not always accurate or up to date. This is apparently what happened as instead of ISIS releasing the address of a Navy pilot, listed the address of a home owned by an elderly couple.
The solution to this problem, as related to me by a retired high level special forces member, is simple. “I think they are seriously underestimating the people they are targeting,” he said. “Many of us have combat experience… and are armed.”
US service members put too much personal information on social media websites and the military releases too much information about troops and what they are doing. In addition to scrubbing this information from websites (which could help but may not be totally effective) the solution is simple. Make it legal for and provide for those targeted with arms!
In the name of political correctness base security has been altered to make them more “civilian friendly”. It is time again to allow our troops on base to carry weapons. Also those service members who have been publicly listed by ISIS should be immediately provided a conceal carry permit for the state that they are in (if they do not already own one).
“Home grown” terrorists will think twice before taking on armed US military personnel.