A Memorandum released last week by the Office of Inspector General revealed that numerous “High-Risk” security vulnerabilities were found in the Joint Polar Satellite System’s (JPSS) Ground System.
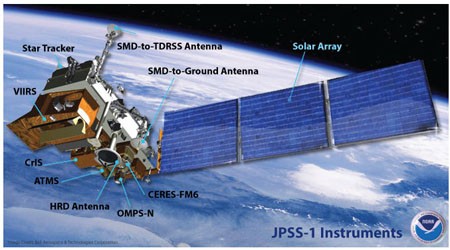
According to the report, a security audit of NOAA’s Information Technology security program found serious security issues with the JPSS Ground System which gathers information from weather satellites and provides it to worldwide users. It also provides command and control for current and future weather satellites.
The system is considered a “High Impact” IT system, or a system “for which the loss of confidentiality, integrity, or availability could be expected to have a severe or catastrophic effect on organizational operations, organizational assets or individuals.”
The report showed that the number of High-Risk vulnerabilities rose from 14,486 in the first quarter of 2012 to 23,868 in the second quarter of 2014:

As you can see from the chart, the vulnerabilities have gone up and down over the last couple years as vulnerabilities have been found and patched. But overall the current vulnerabilities are about 2/3 higher than in the beginning of 2012.
High-Risk vulnerabilities are defined in the report as ones that are “relatively easy for attackers to exploit and gain control over system components.” The vulnerabilities found seem the same as would be found in any corporate security audit and including the following issues:
- Out of date software or missing security patches
- Insecurely configured software
- Unnecessary user privileges
- Passwords and auditing settings do not meet policy standards
- Unnecessary software applications that need to be removed or disabled
The issues found even included the “Heartbleed” vulnerability, which has since been remediated.
The numerous other vulnerabilities are of major concern and the software tools to exploit some of the vulnerabilities are publicly available. For the full report, check out the “Correspondance” PDF link on the Inspector General page.