As the Russia-Georgia War showed us in 2008, there is no love lost between Russia, and Georgia who declared independence from them in 1991. This was actually the second time that Georgia declared independence from Russia. They broke away from Russia in 1918 during the Russian Civil War, only to be attacked by the Red Army and re-absorbed in 1921 during the Soviet-Georgian war.
Georgia claims that Russia is still attacking them, but now in the cyber realm, and they offer as proof, video snapshots of an alleged Russian hacker that was caught in a counter-hack sting!
 Since the Russia-Georgia war in 2008, Georgia has claimed that Russian hackers were infiltrating their computer systems.
Since the Russia-Georgia war in 2008, Georgia has claimed that Russian hackers were infiltrating their computer systems.
The Georgian Computer Emergency Response Team (CERT) has released a 27 page document(Pdf) explaining a Russian Botnet that was detected.
The report also includes a counter-hacking operation that netted a hacker that they claim has ties to the Russian government!
Once infected, according to the report, Russian malware used key word searches for sensitive words inside documents on Georgian machines.
The malware ran from a control panel and uploaded stolen information to command and control servers. The malware was also able to steal certificates, and configuration files, execute remote commands, scan for other targets on the network and most importantly in this case – record audio and video.
The attacks focused on Georgian government sites, critical infrastructure, banks and other non-government organizations. The attacker was able to record live video, and update and modify the malware code from the Command & Control panel.
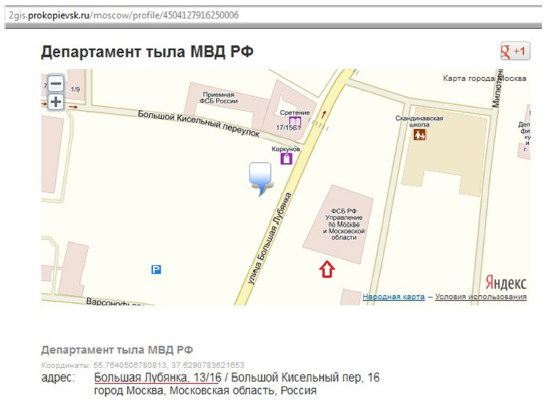
The Georgian CERT team began dissecting and analyzing the malicious attack. When backtracked, one of the domains used in the attack was owned by the Russian Ministry of Internal Affairs, Department of Logistics, which is located right next to the Russian FSB.
Going a step further, they infected one of their own machines with the Botnet and put a tempting file on the computer named “Georgian-Nato Agreement”. This file, according to the report, was infected with the SAME MALWARE that the botnet was using, except this time it connected to Georgian controlled systems!
Unbelievably a suspected Russian hacker fell for it, stealing the file and becoming infected with their own malware. They not only got screenshots of the hacker through his own webcam, but also were able to recover his e-mails, location and even watched him create new modules for the Botnet!
Of course I am sure Russia will deny the allegations, and I doubt the hacker will be arrested, especially if he has ties with the Russian government. But Georgia has some pretty convincing proof.